Post-incident reviews are the key to reducing repeat system failures and improving response times. Without them, teams risk recurring outages, higher costs, and eroded customer trust. Here’s what effective reviews achieve:
- Reduce repeat incidents by 40–60%.
- Recover from outages up to 52% faster.
- Save up to $5,600 per minute in downtime costs.
The process involves analyzing incidents to find root causes, improving workflows, and assigning clear action items. By involving Engineering, Support, and Customer Success teams, you tackle technical issues and customer impacts simultaneously.
Key steps include:
- Collecting detailed incident data (timelines, logs, system changes).
- Conducting a blame-free review meeting with a clear agenda.
- Assigning specific action items with owners and deadlines.
- Tracking progress to ensure long-term improvements.
Teams that follow this structured approach can avoid up to 95% of repeat incidents and build stronger systems over time.
Post-Incident Review: Learn from Incidents Effectively
sbb-itb-e60d259
How to Prepare for a Post-Incident Review
A productive post-incident review starts with solid preparation. Jumping into a meeting without gathering the right data often leads to finger-pointing, guesswork, or missing the actual root cause. The goal is to create a clear and accurate picture of the incident, so the team can focus on understanding why it happened and what needs to change. This involves collecting reliable evidence, assembling the right team, and acting quickly while the details are still fresh.
Collect Incident Data and Documentation
Begin gathering documentation within 24–48 hours after resolving the incident [11]. Delaying this step can cause critical data to disappear, like logs being overwritten, or memories fading, which often leads to speculation. On average, manually reconstructing a postmortem can waste 60–90 minutes per incident as engineers dig through chat logs and system data [10]. That time is better spent on prevention.
Here’s what to collect:
- A detailed timeline: Include UTC timestamps for when alerts were triggered, who responded, the actions taken, and when the issue was resolved [11].
- Technical evidence: This includes error logs, stack traces, monitoring graphs, dashboard snapshots, communication logs (e.g., Slack, Microsoft Teams), war room messages, and customer support tickets. All of these should have accurate timestamps [12][1].
- System change records: Document recent code commits, configuration changes, deployments, and infrastructure updates that happened before the incident [1].
- Impact assessment: Provide exact figures, such as how many users were affected, which services were degraded, error rates, latency spikes, and any revenue or SLA impacts (e.g., 3,241 failed requests) [11][13].
Don’t just focus on what went wrong – also highlight what worked. For example, note which alerts functioned as expected or which safeguards prevented a larger failure. These successes can provide valuable lessons for future incidents [12].
"The timeline is often where the real root cause becomes visible." – Incident Copilot [11]
Modern AI tools can streamline this process significantly. Instead of manually piecing together data from Slack threads and monitoring alerts, AI platforms can generate a comprehensive first draft in about 15 minutes. This draft can include executive summaries, timelines, and impact assessments [10]. These tools automatically pull in Slack messages, alert timestamps, role assignments, and even Zoom call transcripts in real time [10]. For teams managing 20 incidents a month, this approach can save up to $4,500 in engineering time monthly [10]. The AI handles the groundwork, leaving your team to review and refine for accuracy.
Once the data is ready, the next step is to gather the right people to review it.
Bring Together the Right Cross-Functional Team
Post-incident reviews aren’t just for engineers – they require input from multiple teams to get a full understanding of the technical, customer, and business aspects of the incident [8]. Each group brings a unique perspective that contributes to identifying systemic improvements.
From the Engineering team, include those directly involved, such as the Incident Commander, the first on-call responder, and anyone who made key technical decisions [1]. They can explain how the system failed and discuss potential technical solutions [12]. From Support, invite team members who managed customer tickets or escalations during the incident. They’ll provide insights into customer pain points and how the incident impacted trust. From Customer Success, bring someone who can address business impacts, like revenue risks, SLA breaches, or potential customer churn.
You’ll also need a facilitator, someone neutral who wasn’t directly involved in the incident [1]. Their role is to ensure the discussion stays focused on systemic issues rather than individual blame. Facilitators are essential for maintaining psychological safety, which encourages teams to engage in process improvements. Research shows that teams with high psychological safety are 47% more likely to improve processes and 64% more likely to report near-misses [12]. A good facilitator redirects blame-oriented language by asking questions like, “What allowed this to happen?” instead of “Who caused this?” [12].
"This is a blameless post-mortem. We’re here to understand systemic failures, not assign fault. If we find process gaps or unclear documentation, that’s what we fix – not the person who encountered them." – Upstat.io [1]
Create a preliminary document within 48 hours of the incident [15]. It doesn’t need to be perfect – it’s just a starting point to prevent speculation from creeping in. Make sure all logs, graphs, and tickets are stored in a shared location so everyone reviews the same data set [14]. By the time the meeting begins, the focus should be on finding solutions, not debating what happened.
How to Run the Post-Incident Review Meeting
Post-Incident Review Meeting Agenda and Timeline
Once you’ve gathered all the necessary data and assembled your team, the post-incident review meeting becomes the key moment to drive meaningful changes. This meeting is your chance to review the incident thoroughly, validate the timeline, identify systemic issues, and confirm the root cause. The ultimate goal? Define clear steps to prevent similar incidents in the future.
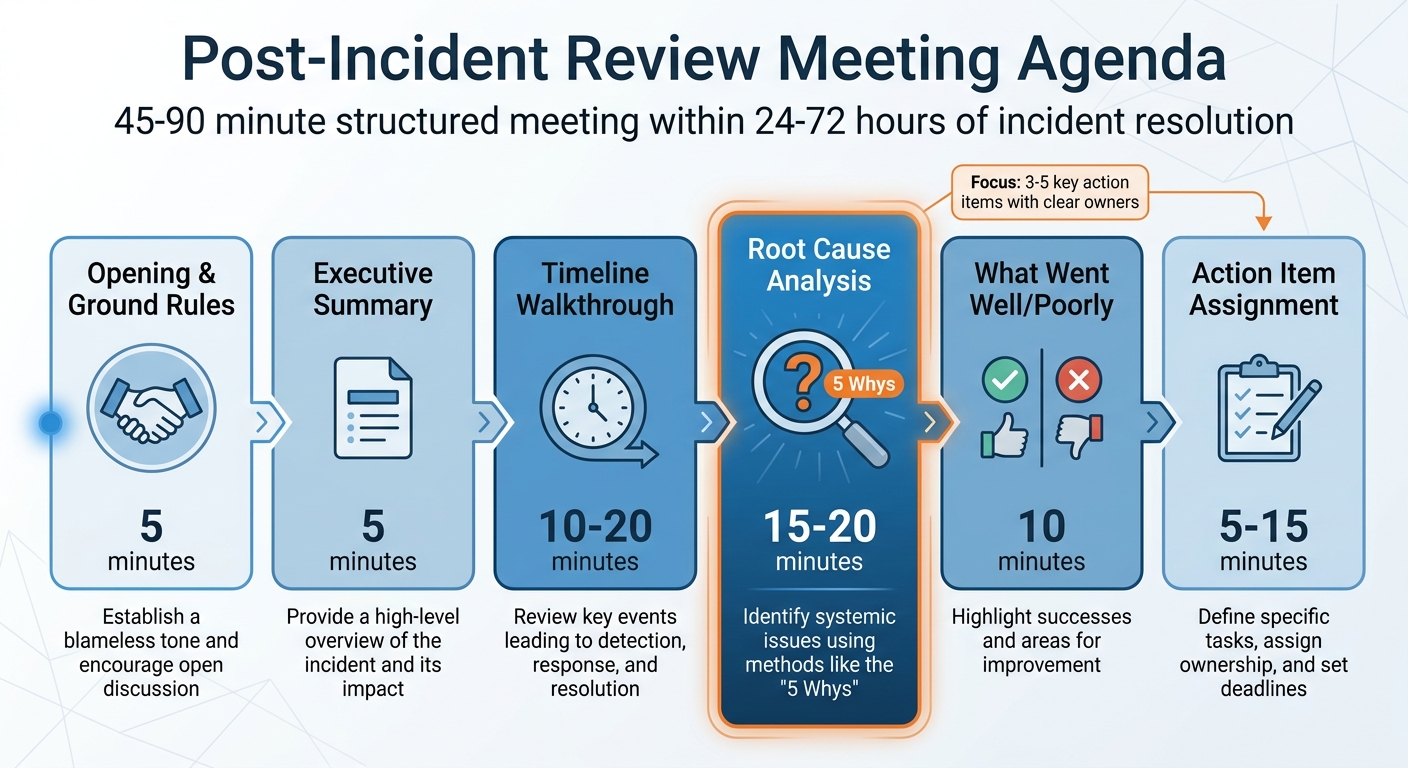
Create an Agenda for the Review
Timing is everything. Schedule the meeting within 24–72 hours of resolving the incident, and plan for 45–90 minutes depending on its complexity[1]. With your data and team ready, a structured agenda ensures the discussion stays focused and actionable. The flow should follow the incident’s timeline, then shift to analysis and planning.
Start with a 5-minute opening to set the tone. The facilitator should clearly communicate the importance of a blameless approach. For instance, they might say, "This meeting is about uncovering systemic issues, not assigning blame. Everyone acted with the best intentions based on the information they had." This creates a psychologically safe environment, which has been shown to boost engagement in process improvements by 47%[12].
Next, dedicate 5 minutes to an executive summary. This is a high-level recap of what went wrong and the business impact. Follow this with a 10–20 minute timeline walkthrough, reviewing the incident’s key events – detection, actions taken, and resolution – in chronological order. Stick to the facts to keep the discussion grounded.
Then, spend 15–20 minutes on root cause analysis. Use tools like the "5 Whys" method to dig deeper into the issue. For example, instead of stopping at "the database went down", explore why it happened – perhaps due to missing documentation or unclear operational limits[6].
Include a 10-minute segment to review what went well and what didn’t. This balanced approach not only highlights areas for improvement but also celebrates successes, like effective alerts or safeguards. Wrap up with 5–15 minutes for action item assignment, focusing on 3–5 key tasks. Assign owners and set deadlines to ensure accountability.
| Item | Duration | Objective |
|---|---|---|
| Opening & Ground Rules | 5 min | Establish a blameless tone and encourage open discussion[1] |
| Executive Summary | 5 min | Provide a high-level overview of the incident and its impact[12] |
| Timeline Walkthrough | 10–20 min | Review key events leading to detection, response, and resolution[1] |
| Root Cause Analysis | 15–20 min | Identify systemic issues using methods like the "5 Whys"[6] |
| What Went Well/Poorly | 10 min | Highlight successes and areas for improvement[1] |
| Action Item Assignment | 5–15 min | Define specific tasks, assign ownership, and set deadlines[1] |
Lead a Blame-Free Discussion
A well-structured agenda is only part of the equation – the facilitator plays a crucial role in guiding the conversation. To maintain neutrality and trust, the facilitator should ideally be someone who wasn’t directly involved in the incident, such as the incident commander or a key decision-maker.
The language you use is just as important as the agenda. Avoid framing questions in ways that assign blame. Instead of asking, "Who deployed that?" try, "What process allowed this change to reach production?" Similarly, replace "Why did you miss the alert?" with "What signals were available at the time?" This shift from "Who" and "Why" to "What" and "How" helps keep the focus on processes rather than individuals[17][18].
If blame does arise, reframe it as a process issue rather than a personal failing. For example, if someone blames themselves, acknowledge their feelings briefly and steer the conversation back to systemic improvements[19].
Finally, make sure quieter team members – like junior engineers or Support staff – have a chance to speak. Their insights can provide valuable perspectives, especially regarding customer-facing impacts that others might not have witnessed[17]. By fostering an inclusive discussion, you ensure all aspects of the incident are considered.
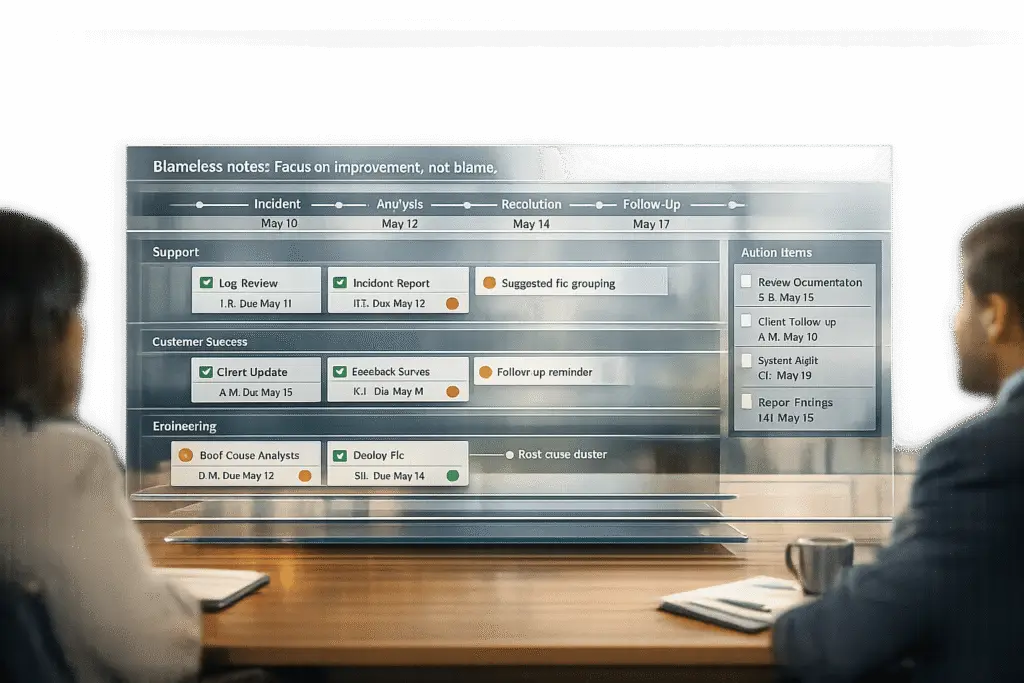
Document Findings and Assign Ownership
To ensure that insights from post-incident reviews lead to meaningful change, proper documentation and clear ownership are key. Without them, even the most insightful findings can fail to create impact. A common pitfall is producing detailed reports that result in no tangible action or improvement.[20]
Write an Action Items Document
After a thorough discussion, it’s crucial to translate insights into specific, actionable tasks. Each action item should include three core elements: the root cause, key learnings, and detailed tasks. Avoid vague instructions – be precise. For example, instead of saying, "Improve monitoring", specify: "Add latency alerting on the payments service for P99 > 500ms."[1]
When investigating issues like a database outage, dig deep to uncover the root cause. For instance, you might find a process gap caused by missing documentation or unclear escalation protocols. Modern AI tools can assist by piecing together timelines from Slack chats and incident logs, but always double-check AI-generated drafts for accuracy.[11]
To prioritize effectively, categorize tasks into three groups: "Must-fix", "Should-fix," and "Nice-to-have." High-performing teams concentrate on completing 3–5 critical tasks rather than overwhelming themselves with exhaustive lists. By focusing on these priorities, teams can reduce recurring incidents by 40–60%.[11]
Assign Owners and Set Deadlines
Defining tasks is just the beginning – assigning clear ownership ensures they get done. Each action item should include five elements:
- A specific owner (by name, not group)
- An action-oriented verb
- A measurable outcome
- Integration into your team’s task tracker
- A clear deadline [20]
Use direct, verifiable verbs like "add", "remove", "deploy", or "change." Avoid ambiguous terms like "investigate", "review", or "improve", which make it harder to confirm task completion. For instance, "Jordan will deploy the new database connection pooling configuration by March 15, 2026" is much clearer and more actionable than saying, "The team will investigate database performance issues."[20]
For larger, systemic problems – like hiring gaps or structural challenges – frame tasks as specific requests for leadership, complete with measurable outcomes and deadlines.[20]
To streamline execution, integrate tasks directly into tools your team already uses, such as Jira, Linear, or Asana. Elite teams aim for a completion rate of 85% or higher for their post-mortem action items, sticking to deadlines.[15] To keep progress on track, the incident owner should send a quick follow-up two weeks after the review.[20]
Follow Up and Track Improvements
Completing the review cycle isn’t just about assigning tasks – it’s about ensuring those tasks lead to real change and strengthen your team’s ability to handle future challenges. Without consistent follow-up, even the best reviews can end up as mere paperwork instead of driving meaningful progress.
Track Progress and Monitor Results
Action items only make a difference when they’re followed through. AI-powered tools can automatically sync action items to platforms like Jira, Linear, or GitHub Issues the moment a post-mortem is approved[21][6]. These tools also provide dashboards that let you filter and monitor statuses such as "In progress", "In review", and "Completed", making it easier for leaders to spot delays or bottlenecks[16][21]. Automated reminders keep teams on track by notifying them as deadlines approach.
Top-performing teams aim for an action item closure rate of 85% or more within set deadlines[15]. To hit this target, it’s crucial to measure both the completion rate and how long it takes to close each item. If you’re seeing a repeat incident rate above 30%, it’s a sign that your post-mortems are creating reports but not driving real learning[5]. AI tools can help by analyzing incident logs to uncover recurring issues, such as systemic failures or misconfigurations, so you can address root causes instead of just patching symptoms[15][10].
Build a Culture of Ongoing Learning
Tracking progress is important, but the real value comes from embedding the lessons learned into your team’s daily operations. Post-incident reviews are only effective when they lead to changes in behavior that reduce the likelihood of future issues[3]. High-performing teams that consistently implement improvements after incidents can reduce repeat incidents by as much as 50%[4].
Take time to analyze near-misses – incidents that were resolved before escalating – to identify gaps in training or weaknesses in alerting systems. These smaller issues often highlight problems that could lead to major outages if left unaddressed[7][3]. Additionally, conducting quarterly trend analyses by aggregating data from multiple reviews can help pinpoint recurring themes and areas for improvement. Sharing anonymized post-mortem findings across teams promotes transparency and encourages collaboration.
"A funny thing happens when engineers feel safe to give details about mistakes, they actually become more accountable and the whole company gets better." – John Allspaw, former CTO of Etsy[4]
Treat post-incident fixes with the same level of importance as new feature development. Set Service Level Objectives (SLOs) for action items, such as completing high-priority tasks within 4–8 weeks[4][15]. When reliability work is prioritized alongside feature development, your team moves away from a reactive, firefighting approach and starts focusing on creating systems that are built to last.
Conclusion
Effective post-incident reviews aren’t about jumping through hoops – they’re about building systems that stop the same issues from cropping up again. The key difference between teams stuck in reactive cycles and those that grow lies in four main practices: thorough preparation, cross-functional collaboration, clear action items, and consistent follow-through.
The numbers back this up. Teams with strong incident response processes resolve problems up to 40% faster and deal with as much as 2.5x fewer repeat incidents. Over time, this can cut future incident rates by as much as 50% [9][2][4]. These stats highlight how critical it is to stick to the process.
If your team is completing fewer than 70% of action items, it’s a red flag that your reviews aren’t leading to real improvements [2]. And if repeat incidents climb above 30%, it’s a sign that you’re just creating documentation rather than learning from mistakes [5]. These aren’t just numbers – they’re indicators that your reviews might be veering off course.
"A well-run postmortem isn’t bureaucratic paperwork. It’s the single highest-leverage activity your engineering team can do after an incident." – API Status Check [2]
FAQs
Who should attend the post-incident review?
The post-incident review process should bring together all teams involved in responding to the incident – this includes support, customer success (CS), engineering, and any other key stakeholders. Working together ensures a detailed examination of the incident, covering everything from its root causes to its overall impact. It also encourages accountability across the board. By taking this collaborative approach, teams can pinpoint corrective actions and work toward improving processes to reduce the chances of similar issues happening again.
How can we identify the root cause without blaming individuals?
To identify the root cause without pointing fingers, concentrate on system-wide factors instead of personal errors. Take a no-blame approach to analyze how elements like system design, processes, or communication breakdowns may have played a role in the incident. For example, ask questions such as, "What circumstances made this mistake possible?" This method encourages openness, builds trust, and supports ongoing improvement by addressing the real issues and reducing the likelihood of future problems.
How do we make sure action items actually get finished?
To make sure tasks are completed after a post-incident review, assign specific owners and set firm deadlines for each action item. This prevents tasks from falling into the dreaded "action item void." Use tools like project management software or schedule follow-up meetings to track progress effectively. Regularly revisiting open tasks in future meetings helps maintain accountability and ensures nothing slips through the cracks. Consistency in follow-ups and a clear process are essential for keeping things on track and achieving meaningful results.