Slack‘s Shared Channels are a compliance risk for businesses handling sensitive data. While they enable external collaboration, they bring challenges like data exposure, weak access controls, and regulatory failures. Organizations using Shared Channels take on legal responsibility for all data shared, including by external participants, which complicates compliance with frameworks like GDPR, HIPAA, and SOC 2.
Key takeaways:
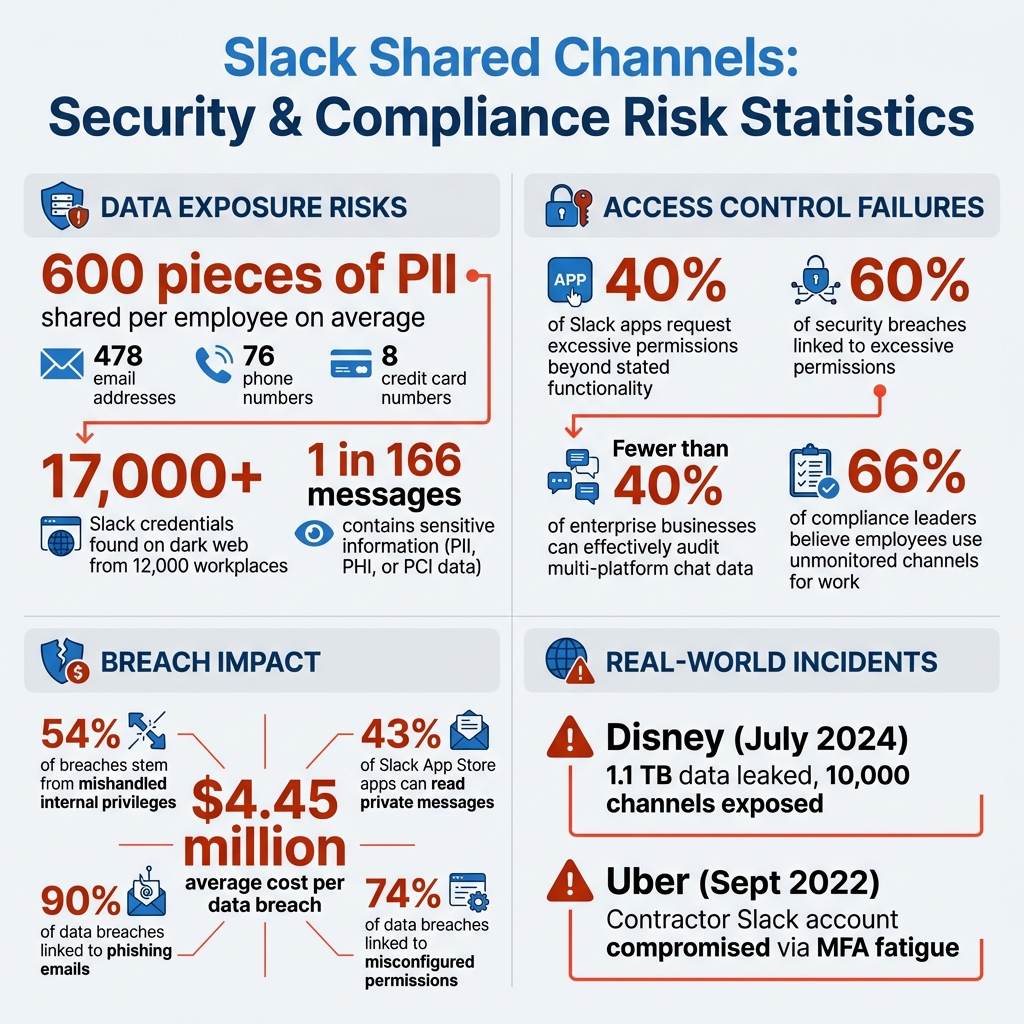
- Data risks: Employees share an average of 600 pieces of sensitive information on Slack, including PII and PHI, which external collaborators can access without strict oversight.
- Access issues: Host organizations can’t fully control external participants’ actions, retention policies, or message deletions, creating compliance gaps.
- Regulatory failures: Retention policies and data deletion processes often conflict with regulations like GDPR, leaving businesses vulnerable to audits and fines.
- Security vulnerabilities: Misconfigured channels, excessive permissions, and third-party app integrations increase the risk of breaches, as seen in Disney’s 2024 Slack-related data leak.
If your business relies on Slack for B2B operations, consider stricter access controls, AI-driven compliance tools, and alternatives like Supportbench for secure communication. These steps can help minimize risk and maintain compliance while collaborating externally.
Slack Shared Channels Security Risks: Key Statistics and Compliance Vulnerabilities
Main Security Vulnerabilities in Slack‘s Shared Channels
Data Privacy and Exposure Risks
Shared Channels in Slack pose considerable risks when it comes to data exposure. On average, employees share 600 pieces of Personally Identifiable Information (PII) on Slack, including 478 email addresses, 76 phone numbers, and 8 credit card numbers [7]. In Shared Channels, external partners gain access to this data without undergoing the same level of internal verification or monitoring [10][2].
Adding to the challenge, the host organization bears full legal responsibility for all data shared within the channel. However, it has no control over how external participants handle or distribute that data. Public link sharing compounds this issue – users often generate public URLs for files or messages, making sensitive information accessible to anyone with the link [8][10]. Alarmingly, cybersecurity researchers have discovered more than 17,000 Slack credentials from 12,000 different workplaces being sold on hacking forums and the dark web [7].
Slack’s policy of retaining all data indefinitely only exacerbates the problem. Even small teams can generate hundreds of thousands of messages each year, creating a massive repository of searchable content that often includes confidential or sensitive information [8]. Depending on the Slack plan, employees may have the ability to search and export years of message history, which could inadvertently expose proprietary information to unauthorized individuals [8][9].
Access Control Weaknesses
Beyond the risks of data exposure, Slack’s Shared Channels reveal critical gaps in access controls. While host organizations can set retention policies, these rules apply only to messages sent by their own team members. Messages from external partners follow the partner organization’s retention policies, which may leave sensitive business data exposed far beyond the host’s compliance timelines [13].
Another issue arises with content management. Organizations cannot edit or delete messages sent by external participants, creating accountability gaps that auditors frequently flag [13]. Additionally, standard data exports from Shared Channels do not include a comprehensive list of external members, making it difficult to track who accessed sensitive information [13].
Bot and integration permissions further complicate security. Research shows that 40% of apps in enterprise Slack environments request permissions that go beyond their stated functionality [11]. These bots often inherit the privileges of the users they interact with, meaning a bot could gain unintended access to sensitive data if it interacts with a high-level user. In fact, 60% of security breaches are linked to excessive permissions [11].
A notable case in mid-2024 highlighted the dangers of unapproved tools. A Slack administrator installed a Generative AI tool with broad OAuth permissions. This tool gained unauthorized administrative access to the organization’s connected Salesforce instance, creating a high-risk data leakage pathway between SaaS platforms that bypassed Slack’s native monitoring [10].
Regulatory Compliance Failures in Shared Channels
The vulnerabilities in Slack’s Shared Channels often lead to significant compliance issues. For example, one in every 166 Slack messages contains sensitive information, such as PII, Protected Health Information (PHI), or Payment Card Industry (PCI) data [17]. Organizations handling PHI must execute a Business Associate Agreement (BAA) with Slack to meet HIPAA requirements. However, many fail to do so, as sensitive data often appears in unconventional fields like file names, custom emojis, or user profiles – areas not covered by standard encryption or BAAs [15].
The General Data Protection Regulation (GDPR) also presents challenges, particularly with the "right to be forgotten." Retention policies set by one organization apply only to their members’ messages. External partners, however, retain their own copies of the data, potentially violating GDPR’s strict timelines for data deletion [14][16]. Studies show that fewer than 40% of enterprise businesses can effectively audit or manage data shared across multiple chat platforms [16].
Access control failures add to these compliance challenges. Audit findings frequently reveal "guest sprawl", where multi-channel guest accounts or former employees retain access to sensitive conversations due to poorly configured identity syncs or skipped access reviews [14][16]. While Slack encrypts data both in transit and at rest, it does not offer end-to-end encryption by default. This leaves data accessible at the server level, falling short of the security requirements demanded by some high-security frameworks [17].
"Slack feels informal, but its backend is deeply integrated with your infrastructure. Security risks often hide not in how Slack is used, but how it’s connected."
– Dvir Shimon Sasson, Director of Security Research, Reco [14]
When official channels become too restrictive due to compliance controls, employees often resort to unmonitored personal apps for business communication. This practice, known as "shadow messaging", removes data from the company’s audit and retention systems. Unsurprisingly, 66% of compliance leaders believe employees use unmonitored channels for work-related discussions, creating blind spots that undermine compliance efforts [16].
sbb-itb-e60d259
Examples of Compliance Failures Linked to Shared Channels
Case Study: Data Breach from Misconfigured Shared Channels
In July 2024, The Walt Disney Company suffered a data breach that highlighted the risks of misconfigured Slack environments. A cybercriminal group, NullBulge, managed to exfiltrate 1.1 terabytes of sensitive data from Disney’s internal Slack workspace. This breach stemmed from a compromised laptop infected with malware and an account with excessive permissions, which exposed 10,000 channels. What could have been a minor incident spiraled into a major data leak due to these vulnerabilities [18][19].
"Slack’s security wasn’t broken, but rather it was a breach enabled by a user who was, at best, granted too much access and, at worst, was an active participant."
– Sanford Bingham, Founder and President, FileOpen Systems Inc. [18]
Shared Channels amplify risks because external participants gain channel visibility without undergoing the same rigorous vetting as internal users. A similar case occurred at Uber in September 2022, where an attacker exploited MFA fatigue tactics to compromise a contractor’s Slack account. This access was then used to infiltrate Uber’s AWS and Google Workspace environments [19][20]. The incident underscores how Shared Channels can act as gateways for broader infrastructure breaches when multi-factor authentication isn’t enforced. Audit teams have repeatedly flagged these vulnerabilities in Slack Shared Channels, emphasizing the need for stricter compliance measures.
Audit Findings: Data Retention Policy Gaps
The breaches above highlight another recurring issue: gaps in data retention policies. Slack’s default setting retains all messages and files indefinitely, which can conflict with data minimization requirements under regulations like GDPR, HIPAA, or SOX [14][7]. The problem becomes more complex in Shared Channels, where retention policies are not uniformly applied. The host organization might enforce specific rules, but external partners’ data is governed by their own policies [13].
Security audits often reveal that legacy messages retained in Slack create additional risks. These messages can expose sensitive information, such as incident timelines, credentials, or system designs. In one documented case, technical discussions in Shared Channels inadvertently left source code snippets, internal links, and API keys searchable years after the project concluded [14].
The 2022 Rockstar Games breach highlighted another compliance failure when contractor access wasn’t revoked after project completion, violating basic access control practices [6]. These findings show how inadequate access reviews and inconsistent retention policies leave organizations vulnerable.
"Slack users (custodians) retain full control over the messages they send and can edit or delete them at any point. This makes it harder for compliance officers to understand when potential breaches might have happened."
– Emily Schwenke, Mimecast [20]
eDiscovery requests add another layer of complexity. Differences in visibility settings across public channels, private channels, and direct messages make it difficult to locate relevant information during audits. When external partners are involved, the challenge grows – standard data exports from Shared Channels often omit detailed lists of external members, complicating efforts to track who accessed sensitive data at specific times [13][20]. These challenges highlight the urgent need for stronger internal controls and alternative workflows to mitigate the risks inherent in Shared Channels.
How to Reduce Risks in Shared Channels
Using AI-Driven Monitoring and Reporting Tools
With employees sending 30–40 messages daily, manual oversight just isn’t practical. That’s where AI-driven monitoring tools step in, catching compliance violations in real time [20]. These tools go beyond traditional keyword filters, analyzing conversations to flag risks that might otherwise slip through the cracks.
Take Mimecast Aware, for example. This platform uses natural language processing (NLP) to monitor Slack messages as they’re sent, identifying potential violations with fewer false positives compared to older detection methods [20]. It connects via API to provide a complete audit trail, even capturing messages that users edit or delete.
"Mimecast Aware’s AI-powered platform was designed to reduce risk and extract value from employee collaboration data in Slack and other tools using proprietary natural language processing (NLP) that surfaces more events with fewer false positives."
– Emily Schwenke, Mimecast [20]
Slack’s AI Guardrails framework adds another layer of protection by using real-time filters and content thresholds. These features help identify security threats like prompt injection attacks and workplace issues such as discrimination or misconduct [3]. Meanwhile, Slack’s Real-Time Search (RTS) API ensures that when access to sensitive documents is revoked, the change is immediately reflected across AI systems [3].
Automated remediation tools enhance compliance further. For example, AI can "tombstone" non-compliant messages – removing them temporarily for review – or provide instant coaching to employees when violations occur [20]. Considering that roughly 90% of data breaches are linked to phishing emails, automated URL filtering within collaboration apps has become a must-have [5].
To complement these monitoring tools, precise access controls are essential for reducing risks.
Setting Up Granular Access Controls
Broad permissions are often the root cause of breaches in Shared Channels. In fact, more than 60% of security breaches are tied to excessive or outdated access rights, and 54% stem from mishandled internal privileges [11]. To counter this, applying the Principle of Least Privilege (PoLP) is critical for every integration, bot, and external connection.
Instead of relying on legacy tokens with broad authority, map access to specific scopes, such as channels:read or chat:write. Research shows that over 40% of apps in enterprise settings request at least one unnecessary permission [11]. Conduct quarterly audits to remove outdated permissions – companies that enforce regular access reviews have cut insider threats by 50% [11].
Role-Based Access Control (RBAC) is another key strategy. By categorizing users into roles like administrators, maintainers, and general contributors, you can ensure that each role has only the permissions they need. For Shared Channels, configure organization-wide settings for invitation approvals and tailor permissions for external organizations based on the nature of the business relationship.
To further minimize risks, block high-risk features like file uploads, canvas sharing, or specific workflows in Shared Channels. For sensitive data, such as Protected Health Information (PHI), set channels to private and enforce multi-factor authentication. Teams that regularly review chat automation rights have been able to reduce external breach risks by 38% [11].
These access controls work hand-in-hand with AI monitoring tools, ensuring secure and role-specific access across integrated systems.
Better Alternatives to Shared Channels for B2B Support Teams
Even with advanced AI monitoring and granular access controls, Shared Channels may not meet the stringent compliance needs of B2B support teams. These teams often handle complex accounts, long-term cases, and renewal-driven relationships, which require platforms specifically designed for secure communication and detailed audit trails.
Supportbench is one such platform, offering a centralized system for managing email, portal, and chat interactions. It provides robust audit logs and version control, while its built-in AI features assist with case summaries, resolution suggestions, and knowledge management – addressing the inconsistencies often seen in Shared Channels.
For organizations that continue to use Slack, real-time Data Loss Prevention (DLP) solutions can help monitor, redact, and manage sensitive information like PII, PHI, and PCI across external communications [20][2]. Enterprise Key Management (EKM) adds another layer of security, allowing organizations to encrypt data with their own keys and revoke access whenever needed [5][20].
Automated e-discovery and archiving strategies are also critical. Instead of relying solely on Slack’s retention policies, external messages and files can be stored securely in third-party data warehouses for compliance auditing [5][20]. Centralized governance dashboards enable administrators to track who initiated connections, who approved them, and monitor suspicious activity – all from a single interface [5].
Slack DLP (Data Loss Prevention): How to protect Slack Workspace from security and compliance risks?
Compliance Checklist for Slack Shared Channels
When using Slack Shared Channels in B2B support operations, having a detailed checklist is essential to meet compliance standards.
Questions to Ask During Compliance Reviews
Before your next audit, sit down with your security team and address these critical questions:
- Can you verify who approved each external connection? Ensure that external connection approvals are managed through strict organization-wide settings [22].
- Are you tracking what external users can actually do? Make sure you monitor external user activities and set posting permissions to "post only" to limit their access [12].
- Do you know where your data lives? Organizations handling regulated data must confirm that their data residency settings comply with local regulations [1][20].
- Can you prove retention policies are working? Check that retention policies are active, while noting that these only apply to messages from your members [13].
- Are third-party apps vetted before installation? With 43% of Slack App Store apps capable of reading private messages, enabling "Require App Approval" is a must [6].
- Can you capture the complete message history? Since Slack users control edits and deletions, third-party compliance tools are needed to maintain an unalterable record [20].
Answering these questions lays the groundwork for configuring your Shared Channels securely.
Configuration Checklist for Secure Shared Channels
To keep your Shared Channels secure, focus on these key configurations:
- Enforce identity verification through multi-factor authentication (MFA) or single sign-on (SSO) with trusted providers [21][20].
- Restrict file and canvas sharing in Shared Channels using Slack Connect settings to minimize risks of data exfiltration [22].
- Set up automated anomaly responses to terminate user sessions if suspicious activities occur, such as data scraping, excessive downloads, or access from Tor exit nodes [23].
- Enable native DLP rules for Slack Connect to scan for sensitive information like credit card numbers or email addresses. Use Slackbot for daily violation summaries to ensure quick admin responses [24].
- Integrate the Audit Logs API with your SIEM to track malicious access attempts in real time [4].
- Review app scopes quarterly. Categorize app scopes by risk level, and require executive approval for high-risk scopes such as
admin.*,search:read, orfiles:read[6].
As Dvir Shimon Sasson, Director of Security Research at Reco, emphasizes:
"OAuth Is Often the Weakest Link: Most Slack compromises stem from OAuth abuse – review every integration like you would a cloud IAM role." [6]
Conclusion
Summary of Shared Channel Vulnerabilities
Slack’s Shared Channels reveal some serious compliance challenges. While Slack ensures the security of its infrastructure, the responsibility for enforcing proper configuration, monitoring, and management falls squarely on the organizations using it – a task many find difficult to handle effectively [9]. The absence of end-to-end encryption leaves sensitive data vulnerable at the server level [17]. Moreover, access controls are tied to broad workspace permissions, and third-party apps have the potential to access private messages [6]. Indefinite retention policies only heighten the risk, and stolen tokens can bypass multi-factor authentication altogether. These factors make Slack unsuitable for regulated B2B support environments [25].
The Disney breach in July 2024, which resulted in significant data loss, highlights how quickly informal collaboration tools can turn into compliance hazards [25][9]. As Snehal Antani, CEO of Horizon3.ai, warned:
"When your internal R&D roadmap, contract details, and credentials are all in Slack, a single compromise can derail the business" [25].
These risks make it clear that organizations must prioritize collaboration tools built to meet strict regulatory standards.
Choosing Secure Collaboration Tools for B2B Teams
To address these vulnerabilities, businesses need to shift toward tools designed with compliance at their core. If your organization deals with regulated data, manages complex B2B accounts, or frequently undergoes audits, it’s critical to evaluate platforms that prioritize security and compliance. For instance, tools like Supportbench provide features such as immutable recordkeeping (preventing user edits or deletions), granular role-based access controls, and integrated AI functionalities that reduce the dependency on third-party apps [26].
This transition from casual chat-based tools to compliance-focused systems isn’t just about meeting audit standards – it’s about safeguarding customer trust and ensuring operational stability. With 74% of data breaches linked to misconfigured permissions and the average breach costing $4.45 million, investing in the essential toolset for modern B2B support teams isn’t just smart – it’s essential for sustainable B2B operations [6].
FAQs
Why do Shared Channels fail security audits?
Shared Channels in Slack frequently stumble during security audits because of weaknesses in data privacy, access control, and regulatory compliance. Collaborating with external parties through these channels introduces risks like data leaks or unauthorized access if safeguards aren’t firmly in place. On top of that, keeping tabs on and auditing these channels can be tricky, as Slack’s design may limit comprehensive security management. Without robust governance and advanced monitoring tools, shared channels can create compliance gaps, making them vulnerable to audit failures.
Who is responsible for data shared with external users?
The organization managing the Slack workspace holds the responsibility for any data shared with external users. While Slack offers various security features and compliance tools to help safeguard information, it’s up to the organization to ensure that data sharing aligns with relevant regulations and adheres to their internal policies.
How can support teams reduce Shared Channel compliance risk?
Support teams can reduce compliance risks in Slack’s Shared Channels by implementing clear usage policies, educating employees on data privacy and access control, and using AI-powered monitoring tools to identify potential weaknesses. Take advantage of Slack’s built-in security features like data retention controls and audit logs, and schedule regular audits to eliminate outdated connections. By blending policy enforcement, smart technology, and consistent monitoring, teams can maintain secure external collaboration while keeping compliance risks in check.
Related Blog Posts
- How do you set up a customer portal that supports role-based access and multiple customer teams?
- How do you evaluate “foreign access risk” when choosing a US vs non-US helpdesk?
- The Hidden Risks of Slack-First Support: Data Retention and Audit Failures
- Visibility Gaps in Slack Support: What VPs Miss When Data Stays in Channels










