When building SaaS platforms for Canada’s public sector, ITSG-33 compliance is mandatory. This framework ensures your software meets government security standards, allowing it to handle sensitive data like Protected A or B information. Without ITSG-33, your platform can’t operate on government networks.
Key takeaways:
- ITSG-33 is a lifecycle-based IT security framework developed by the Canadian Center for Cyber Security.
- It’s essential for obtaining an Authority to Operate (ATO), the approval required to handle government data.
- Compliance includes implementing security controls from ITSG-33’s catalog, focusing on management, technical, and operational safeguards.
- The most common control profile for SaaS platforms is Protected B, Medium Integrity, Medium Availability (PB/M/M), used for data breaches with medium impact risks.
- Security measures include multi-factor authentication (MFA), encryption (e.g., AES-256, TLS), role-based access control (RBAC), and continuous monitoring.
- Ongoing compliance requires integrating security into your development process, conducting regular risk assessments, and automating monitoring and incident response.
ITSG-33: What It Is and How It Works
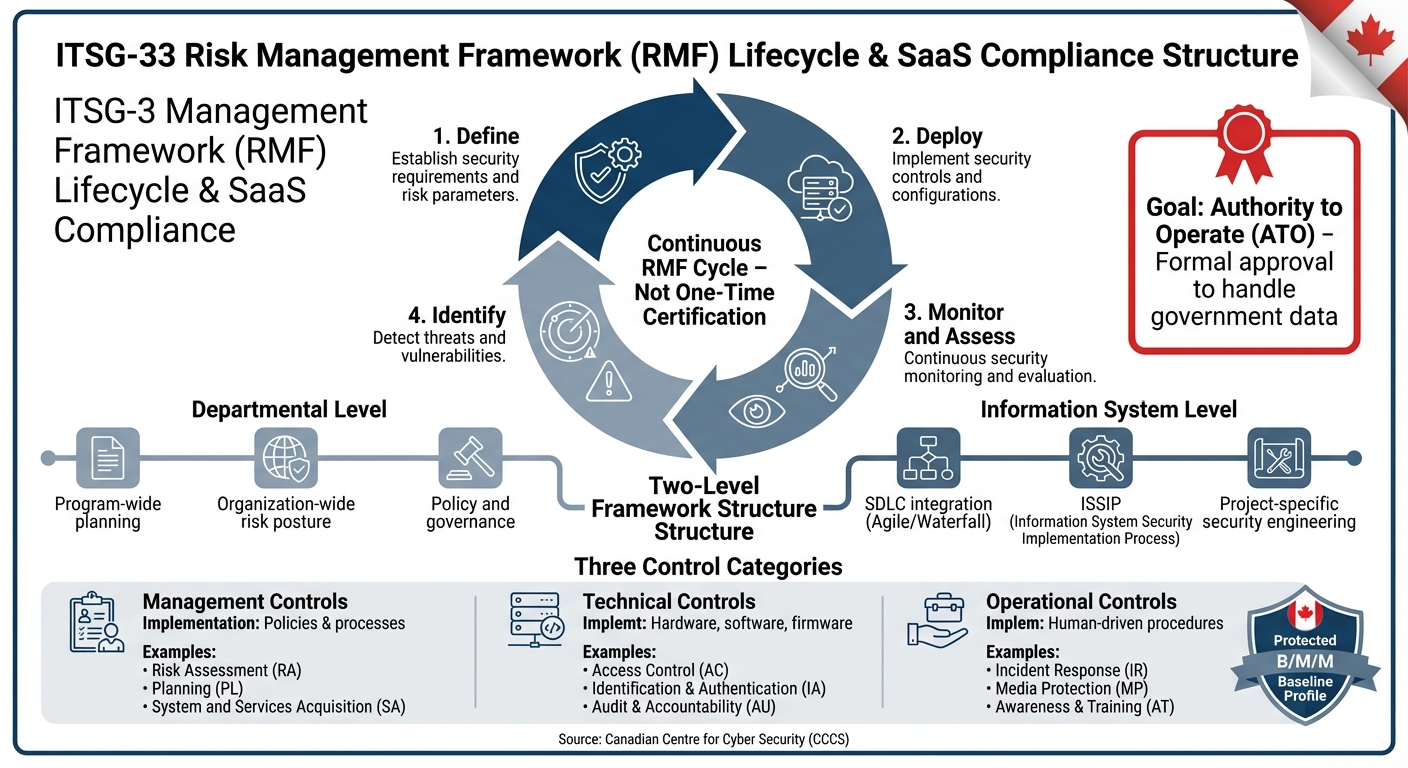
ITSG-33 Risk Management Framework Lifecycle for Canadian SaaS Compliance
What is ITSG-33?
ITSG-33, short for "IT Security Risk Management: A Lifecycle Approach", is a framework developed by the Canadian Centre for Cyber Security (CCCS) to manage IT security risks across Government of Canada (GC) departments. It officially replaced two earlier publications – MG-2 (Security Risk Management) and MG-4 (Certification and Accreditation) – on November 1, 2012.
For SaaS vendors, ITSG-33 compliance is non-negotiable. It’s the foundation for obtaining an "Authority to Operate" (ATO), which is the formal approval needed to legally handle or process government data.
The framework introduces a standardized set of security requirements and terminology for all government departments. This unified approach ensures consistency and helps balance security controls with acceptable levels of residual risk, all while aligning with specific mission priorities.
The Risk Management Framework (RMF)
At its core, ITSG-33 is powered by the Risk Management Framework (RMF), which promotes continuous security across both departmental and system levels. Unlike traditional security models, ITSG-33 shifts from a one-time certification process to an ongoing lifecycle approach – Define, Deploy, Monitor and Assess, and Identify.
The RMF operates on two levels:
- Departmental Level: Focuses on program-wide planning and maintaining an organization-wide risk posture.
- Information System Level: Integrates security engineering into individual projects, aligning with your software development lifecycle (SDLC).
At the system level, the framework incorporates the Information System Security Implementation Process (ISSIP). This process weaves security activities directly into your SDLC – whether Agile or Waterfall – minimizing the need for expensive retrofitting later on.
"By following the principles within this publication, you not only help ensure predictability and cost-effectiveness, you also help ensure that there are no hidden surprises preventing you from obtaining authority to operate." – Canadian Centre for Cyber Security
The ITSG-33 Security Control Catalogue
The Security Control Catalogue is a detailed library of standardized security requirements. These controls are grouped into three main categories: Management, Technical, and Operational.
| Control Class | Implementation Method | Examples |
|---|---|---|
| Management | Policies and management processes | Risk Assessment (RA), Planning (PL), System and Services Acquisition (SA) |
| Technical | Hardware, software, and firmware | Access Control (AC), Identification and Authentication (IA), Audit and Accountability (AU) |
| Operational | Human-driven procedures | Incident Response (IR), Media Protection (MP), Awareness and Training (AT) |
Instead of picking controls one by one, SaaS platforms typically rely on pre-defined Security Control Profiles outlined in Annex 4A. A common choice for GC cloud services is the "Protected B, Medium Integrity, Medium Availability" (PB/M/M) profile. This is designed for data where a breach could cause a "medium level of injury" to non-national interests. These profiles serve as a baseline, which can then be adjusted to fit your technical and business needs.
How ITSG-33 Controls Apply to SaaS Platforms
To align with ITSG-33 guidelines, SaaS providers must first classify their services based on the potential risks to confidentiality, integrity, and availability. This classification helps determine the appropriate security measures. For Canadian public sector SaaS platforms, the Protected B, Medium Integrity, Medium Availability (PB/M/M) profile is often the baseline requirement.
ITSG-33 offers a structured framework for managing risks, and its controls can be adjusted to fit your platform’s specific threat landscape. The Canadian Centre for Cyber Security also allows providers to use existing third-party attestations to map their compliance with ITSG-33. Below, we’ll explore how access controls, encryption, and monitoring measures are applied to secure SaaS platforms under these guidelines.
Access and Authentication Controls
Access control begins with multi-factor authentication (MFA), which is mandatory for all users handling Protected B data, privileged accounts, and remote access solutions. To ensure stronger security, use phishing-resistant MFA options like FIDO2 or hardware tokens instead of SMS or email-based codes.
Your platform should also support federated authentication protocols like SAML or OpenID Connect. This enables government users to log in with their existing enterprise credentials, reducing the risks of password reuse and credential sprawl. However, highly privileged accounts, such as Global Admin or Root, should remain "cloud-only" and excluded from federation to minimize risks if on-premises environments are compromised.
Role-Based Access Control (RBAC) must adhere to the principle of least privilege. This means disabling default and dormant accounts, reviewing role assignments annually, and implementing Just-in-Time (JIT) access for administrative tasks. JIT access ensures roles are activated only for a limited time and require approval. Additionally, passwords must be at least 12 characters long, with no maximum length restrictions.
| Authentication Factor | Description | Examples |
|---|---|---|
| Something you know | Information only the user knows | Passwords, PINs, Passphrases |
| Something you have | Physical items the user possesses | Hardware tokens, Smart cards |
| Something you are | Unique physical characteristics | Fingerprints, Retina scans, Voice patterns |
Encryption and Data Protection
Strong encryption is essential for protecting data integrity. Data must be encrypted both at rest (SC-28) and in transit (SC-8, SC-9) using secure, authenticated protocols. For data at rest, use algorithms like AES-256 and store cryptographic keys separately from the encrypted data. For data in transit, enforce TLS with modern cipher suites and validated certificates. Implement mutual TLS (mTLS) for service-to-service communication to authenticate both endpoints.
"If a connection isn’t authenticated, an attacker could impersonate a trusted system. And if data is authenticated but not encrypted, the contents could still be exposed." – Palo Alto Networks
Adopting a Zero Trust model further strengthens your architecture. In this model, no entity is trusted by default, and access is continuously verified. Use Zone Interface Points (ZIPs) – virtual appliances in cloud environments – to monitor and control data movement between security zones. Administrative tasks should be performed with dedicated accounts that lack internet or email access, and user functionality should be separated from system management tasks.
Secure deletion of expired data is another critical component. For data that has reached the end of its retention period, use media sanitization or secure overwriting to prevent recovery (MP-6). Additionally, Protected B workloads must be hosted within Canada’s geographic boundaries.
Monitoring and Incident Response
Real-time monitoring and centralized logging are essential for identifying and mitigating threats. SaaS platforms must integrate both interactive and non-interactive sign-in logs, as well as privilege change events, into a centralized security monitoring system. This approach supports controls like AU-2 (Auditable Events), AU-12 (Audit Generation), and SI-4 (System Monitoring).
For incident response (IR-4), clearly defined procedures for managing and reporting security breaches are mandatory. Government of Canada departments are required to implement and report compliance with cloud guardrails within 30 business days of accessing a cloud account. To maintain secure operations, it’s recommended to have at least two, but no more than five, registered root or global administrators for a cloud tenant.
How to Achieve ITSG-33 Compliance for Your SaaS Platform
To meet ITSG-33 compliance, you need to weave security into your System Development Life Cycle (SDLC) right from the beginning. By embedding security activities into your workflow through the Information System Security Implementation Process (ISSIP), you ensure that security isn’t an afterthought but a fundamental part of your development process.
Conducting a Threat and Risk Assessment (TRA)
Start by carrying out a Threat and Risk Assessment (TRA) to determine the security controls your platform needs. This involves classifying your SaaS platform based on its potential impact on confidentiality, integrity, and availability. Essentially, you’ll evaluate how sensitive the data you handle is and how critical the business processes you support are.
Create an injury assessment table to define injury levels – ranging from Very Low to Very High. Common injury types include financial loss, reputational damage, privacy breaches, and regulatory penalties. Use the "High Water Mark" principle: assign your overall security category based on the highest risk among the three objectives.
Next, identify potential threat agents and their capabilities. ITSG-33 breaks down deliberate threats into categories from Td1 (basic, non-malicious users) to Td4 (advanced attackers like organized crime using zero-day exploits and social engineering). It also accounts for accidental and natural hazards, categorized from Ta1 to Ta3. Build a detailed inventory of your business processes and information assets – like medical records or financial transactions – so you know exactly what needs protecting.
After implementing the necessary controls from the ITSG-33 catalog, assess the residual risk, which is the risk that remains after controls are in place. This residual risk must typically be "Low" for an authorizer to grant an Authority to Operate (ATO). With risks identified and controls in place, you can integrate these measures into your development lifecycle.
Integrating and Testing Security Controls
Security controls should be integrated during the Detailed Design and Development phases. This is where mechanisms like TLS encryption are built directly into your system’s architecture. By mapping ISSIP activities into your Agile or Waterfall workflows, you ensure that security isn’t sidelined. A Security Requirements Traceability Matrix (SRTM) can help you track these controls from the requirements phase all the way through testing and validation.
Testing security controls happens in two key stages: Integration Security Testing in a controlled test environment, followed by Security Installation Verification (SIV) once the system is live. SIV ensures that your controls remain effective in the production environment. To avoid duplicating efforts, leverage inherent security features in your infrastructure. Automate security testing and vulnerability assessments within your CI/CD pipeline to streamline the process. Document your design specifications to show how your technical measures align with ITSG-33 standards. The intensity of your testing depends on the Robustness Level (RL), which is determined by your data’s sensitivity and the threat landscape.
Maintaining Continuous Compliance
ITSG-33 compliance doesn’t stop once the system is operational. Continuous assessment and immediate response to new threats are key to staying compliant. During the Operations and Maintenance phase of your SDLC, your IT team should regularly monitor and update controls. As the Canadian Centre for Cyber Security explains:
"Continuous improvement is a key aspect of the recommended process to ensure that as the threat environment evolves, so do the controls that have been put into place."
Automate vulnerability scans to simplify compliance efforts and focus on fixing issues quickly. Use automated incident response systems to safeguard data and ensure business continuity. Centralize security configurations, access policies, and encryption management to reduce complexity. Regularly conduct third-party audits to ensure that your controls keep pace with emerging threats.
Generate detailed audit logs automatically to make compliance reporting easier and speed up your response to threats. AI-powered tools for exposure management can also provide a clear view of your security posture, helping you prioritize vulnerabilities based on actual risk levels.
sbb-itb-e60d259
Common Compliance Mistakes and AI-Powered Solutions
Common Compliance Mistakes
Security can’t be an afterthought in development – it needs to be part of every phase, not just a final checkbox. A frequent mistake is failing to integrate ISSIP (Information System Security Implementation Process) into the Software Development Life Cycle (SDLC). Instead, some organizations run security activities separately, bypassing critical stages like requirements analysis, design, and testing. Another misstep is relying on generic security profiles without tailoring them to specific risk environments. ITSG-33 profiles, for instance, are meant to serve as starting points, not comprehensive solutions.
Manual compliance processes also bring their own set of challenges. Take password aging policies as an example. These policies often create a "heavy burden" on users, leading to risky behaviors like writing passwords down. Manual methods also lack the adaptability needed to respond to ever-changing threats. A particularly common oversight is leaving "organization-defined security control parameters" blank instead of customizing them to fit operational realities. Identifying these pitfalls is the first step toward adopting AI-driven solutions that can make compliance more effective and efficient.
Using AI to Reduce Compliance Costs
AI-powered tools are changing the way organizations handle compliance, offering automation to cut down on manual work. For instance, in continuous monitoring (CA-7), AI replaces periodic manual audits with real-time telemetry and anomaly detection. This shift allows organizations to move from static, point-in-time assessments to dynamic, ongoing security management. Similarly, AI-driven audit reduction (AU-7) can sift through massive log volumes, flagging only the events that suggest potential compromises. This dramatically reduces the workload for compliance reporting.
When it comes to authentication, adaptive AI systems (IA-10) take a smarter approach. These systems adjust security requirements in real time based on user behavior and risk scoring, eliminating the inefficiencies of manual password policies. AI also improves the Threat and Risk Assessment process (RA-3) by analyzing emerging threats and forecasting potential vulnerabilities before they become issues. In fast-paced CI/CD cycles, AI automates security impact analysis (CM-4), ensuring compliance is maintained even as platforms rapidly evolve. By embedding AI early in the SDLC – right from the requirements analysis and design phases – organizations can build security controls directly into their projects, cutting both costs and risks.
Conclusion
Meeting ITSG-33 requirements isn’t just about checking a compliance box – it’s about earning and maintaining trust with Canadian public sector clients. By embedding security measures early in the process, SaaS vendors can avoid unexpected compliance hurdles. This proactive approach also creates a shared framework for clearer, more predictable communication with government authorizers and security assessors, leading to fewer delays and reduced costs.
AI-driven solutions are reshaping how compliance is managed. For example, in April 2022, a major cloud provider introduced a Terraform-based Infrastructure-as-Code template tailored for the Canadian public sector. This tool automates the deployment of Protected B Landing Zones in line with ITSG-33 Annex 4A. By replacing manual configurations with automated, codified security settings, SaaS vendors can significantly cut down on implementation time and operational expenses. This automation also supports the continuous vigilance needed to address today’s ever-changing cybersecurity threats.
For SaaS vendors, staying compliant is a continuous effort, especially as the threat landscape evolves. Certifications like SOC 2 Type II or ISO/IEC 27001 not only enhance global credibility but also simplify Canadian evaluations. The Canadian Centre for Cyber Security recognizes these certifications as evidence, helping to streamline the evaluation process. In short, investing in globally recognized standards can open doors and accelerate entry into the Canadian market.
FAQs
How can SaaS platforms achieve ITSG-33 compliance for serving the Canadian public sector?
To meet ITSG-33 compliance, SaaS platforms need to adopt a well-defined security risk management process. Start by determining the sensitivity and impact levels of the data your platform processes. This step helps outline the necessary security controls and identify potential risks, such as vulnerabilities and threats.
Once risks are assessed, implement security controls tailored to those findings and the compliance requirements. These controls should be appropriate for the classification level of the data, whether it’s protected or classified. After implementation, focus on continuous monitoring, incident response planning, and regular updates to address new security challenges. This ongoing approach helps your SaaS platform align with Canadian public sector standards while effectively managing risks.
What does ITSG-33 compliance mean for securing Canadian public sector data?
ITSG-33 compliance offers a structured framework designed to protect sensitive data within the Canadian public sector. By defining robust security controls and risk management practices, it ensures that risks are effectively identified, evaluated, and mitigated throughout a system’s lifecycle. This approach is crucial for securing classified information, such as PROTECTED B or SECRET data, against constantly evolving cyber threats.
Organizations adhering to ITSG-33 implement tailored measures like access management, asset management, and incident response. These measures play a critical role in preventing unauthorized access and data breaches. By doing so, they uphold the confidentiality, integrity, and availability of essential information. Moreover, ITSG-33 aligns security protocols with national standards, helping organizations reduce vulnerabilities and strengthen defenses against cyberattacks.
How does AI help SaaS providers meet ITSG-33 security requirements for the Canadian public sector?
AI is transforming how SaaS providers stay compliant with ITSG-33 by simplifying security processes and improving risk management. It offers tools for real-time monitoring, identifying threats, and responding quickly to vulnerabilities, ensuring that security measures stay effective and in line with ITSG-33 requirements.
By taking over repetitive tasks such as log analysis, compliance verification, and incident response, AI minimizes human error while maintaining constant oversight. This forward-thinking approach helps SaaS providers protect sensitive government data and meet the evolving security demands of Canada’s public sector.










